























From Distributed Signals to Autonomous Defense
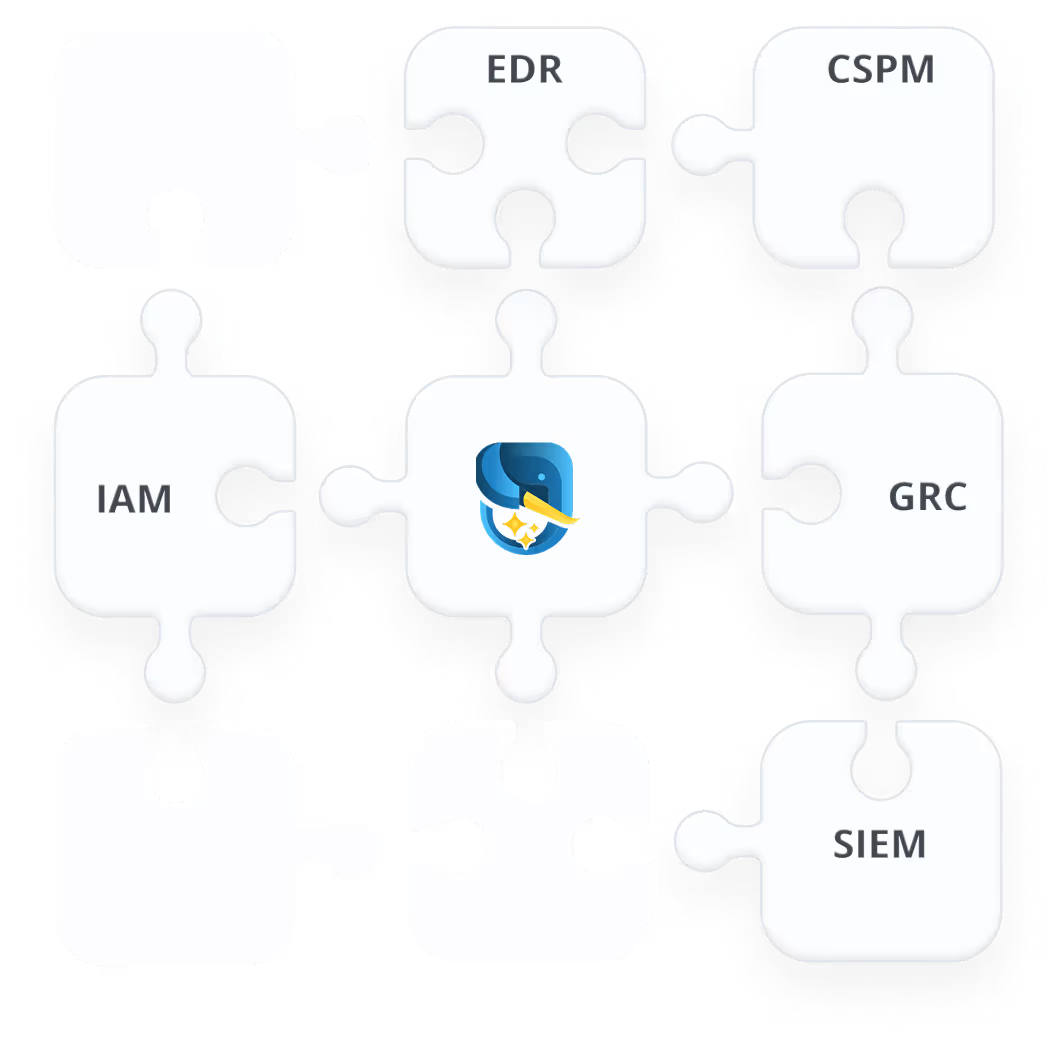
Federated Detection
Run detection logic across the security tools and data sources you already use, without forcing everything into a centralized logging system first.
Outcome: Broader detection coverage with lower SIEM and log-ingestion burden.
.avif)
.avif)
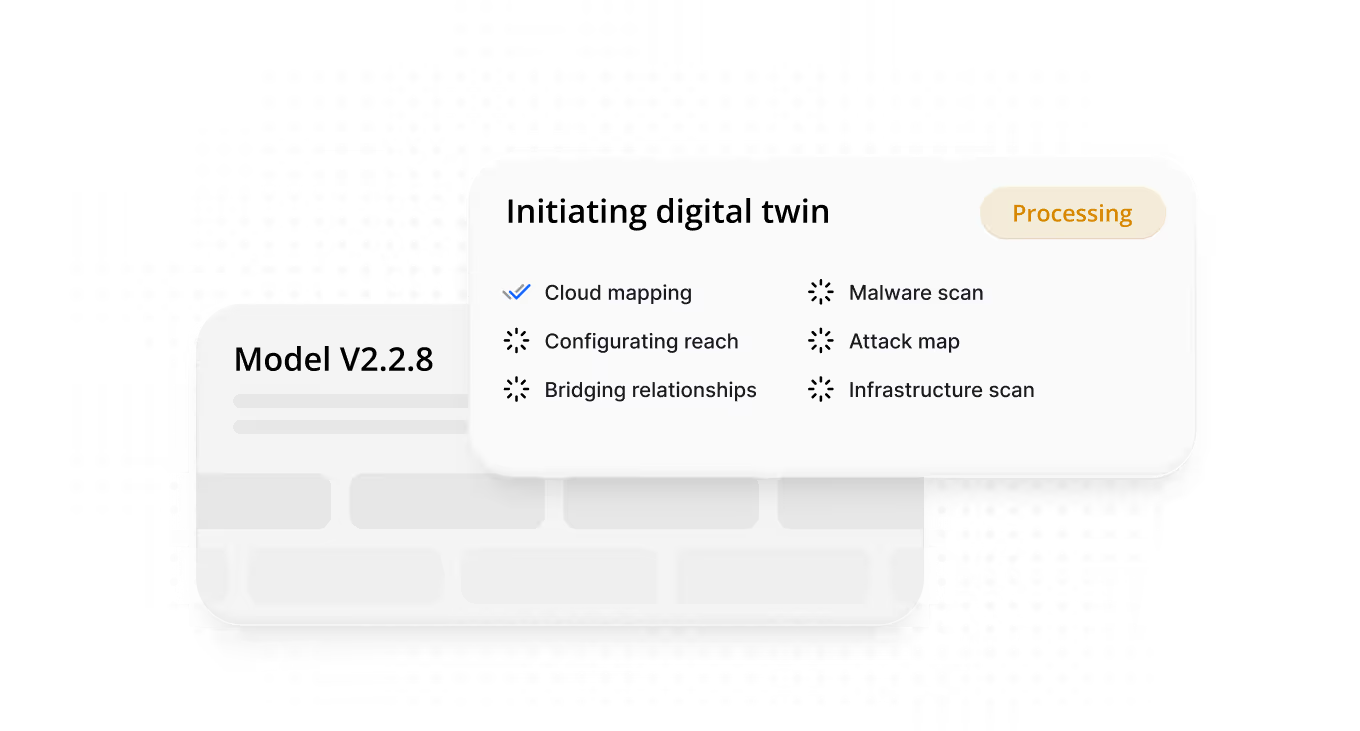
Build Shared Context
Connect identity, endpoint, cloud, and network telemetry into a live Security Context Graph so teams can understand how attacker activity, infrastructure relationships, and control gaps connect across the environment.
Outcome: Full visibility into how attackers could move through your environment today.
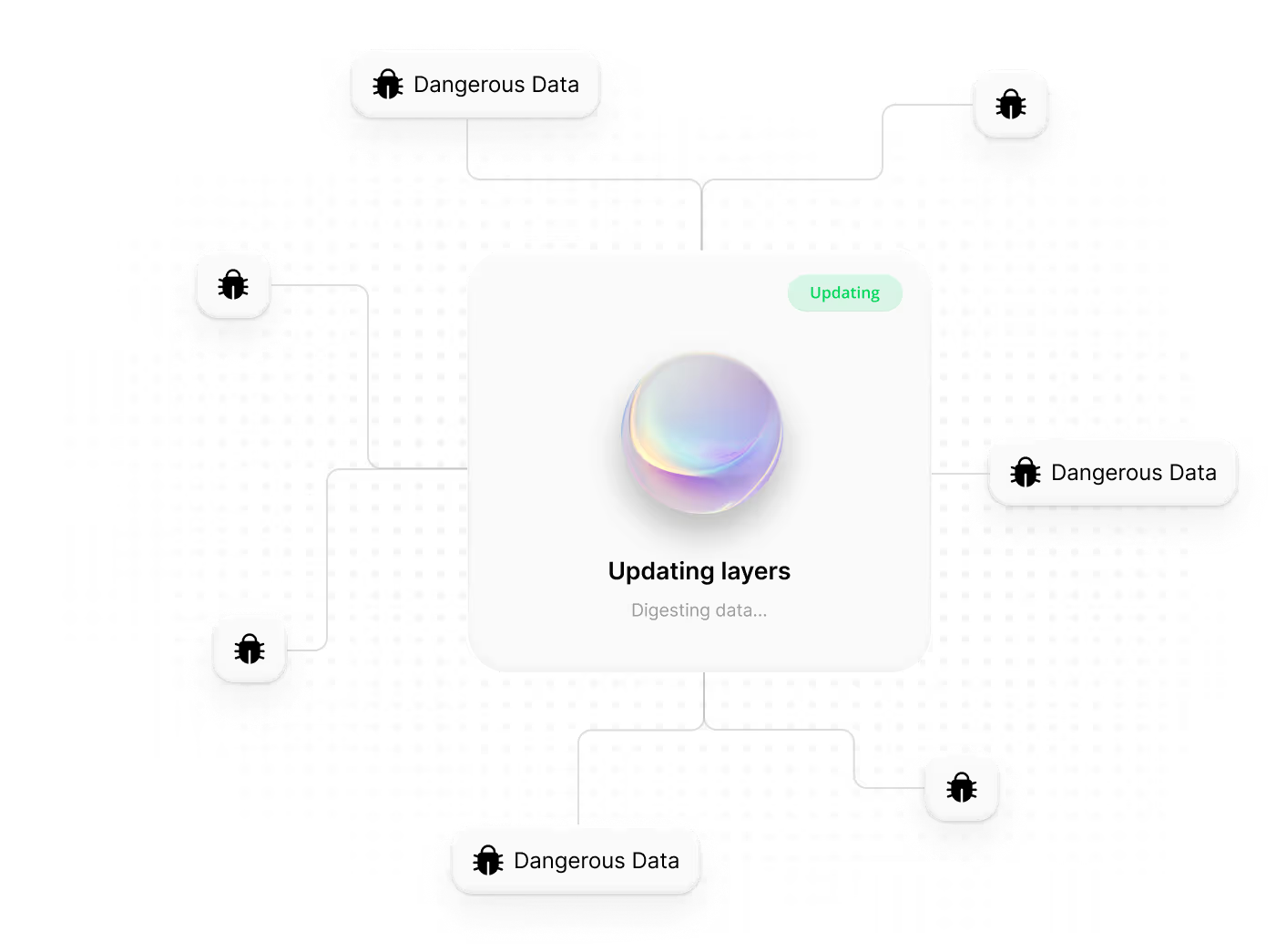
AI-Powered Detection Engineering
Use AI to generate and continuously refine detections as attacker behavior evolves, using available telemetry and system feedback to improve coverage over time.
Outcome: Higher-fidelity detections for multi-stage attacks across distributed environments.
.avif)
.avif)

Autonomous Triage & Hunting
AI Analysts validate detections, filter out false positives, surface hidden attacker behavior, and prioritize what represents real breach risk.
Hunts multi-stage attacker behavior and APT activity across distributed telemetry
Compresses investigation from hours to minutes, closing exploit windows
Outcome: Faster MTTR, reduced analyst noise, and automated Tier 1–3 coverage.
Precision Containment
Pushes targeted response actions back through the tools and controls you already use, while feeding outcomes back into the system so detections and defenses improve over time.
Outcome: Faster containment and a SecOps workflow that gets smarter with every signal.
.avif)

“Data from Tuskira AI demonstrates that an AI agent can handle up to 2,000 security incidents per day — compared to 1,800 to 2,000 for a human analyst per year — freeing human experts to focus on edge cases and high-value anomalies.”
What security leaders are saying
See Full Stack Agentic SecOps in Action
Generate detections at the source, connect them through shared context, and accelerate triage and response across the SOC.

Watch the video
See how Tuskira helps security teams validate threats, uncover breach paths, and move faster from signal to action.

