Agentic Threat Exposure Management
Know which risks are real, and which ones attackers can’t exploit.
Why You Should Care
- Vulnerability lists are noisy and disconnected from real exploitability
- CVSS ignores identity posture, control coverage, and reachability
- Engineering time is spent on theoretical risk
- CISOs need defensible, evidence-backed prioritization
How Tuskira Solves It
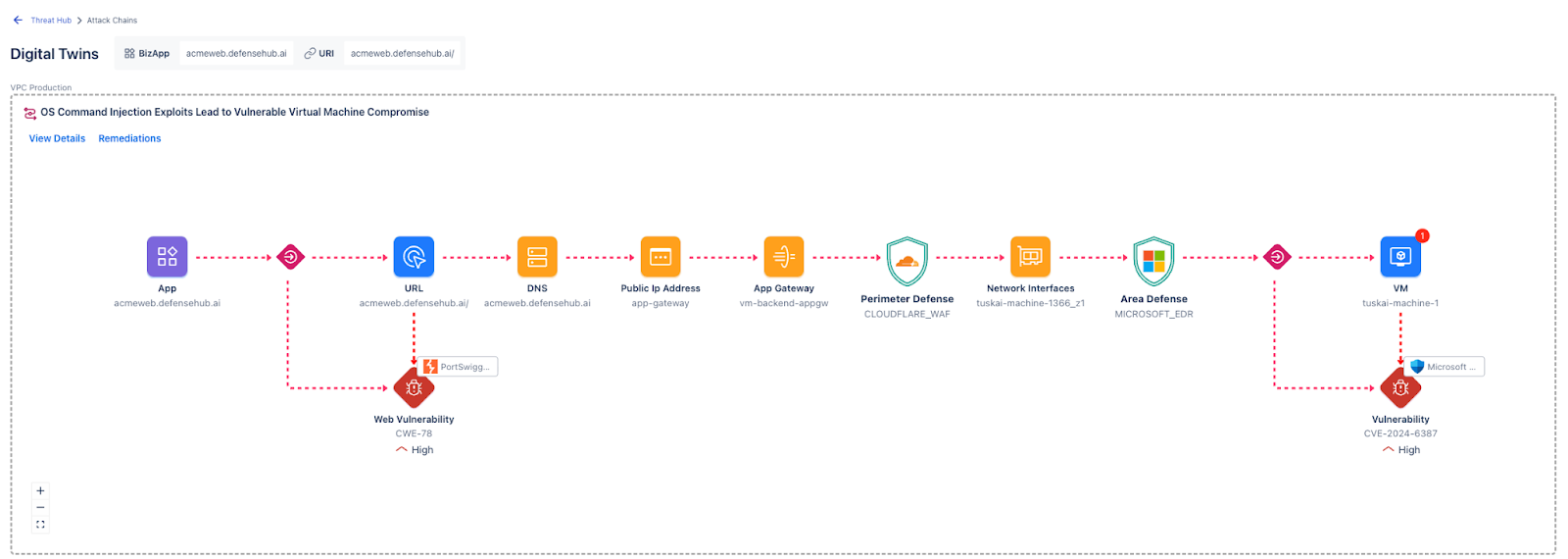
Tuskira replaces severity-based scoring with continuous validation of attack paths in your environment.
- The Twin: A live virtual replica of your infrastructure that maps identities, assets, network paths, and security controls.
- Attack-path validation: AI continuously tests whether exposures are actually reachable
- Defense-first mitigation: When a path is validated, the fastest control change to break it is recommended
- Persistent hardening: Once broken, similar exposure patterns are continuously monitored to prevent recurrence
The output is a ranked set of reachable attack paths, each with specific mitigation steps to close it.
Who benefits
- CTEM and Security Engineering leaders
- Platform and Infrastructure Security teams
- CISOs who need defensible risk reduction beyond scanner output
See Full Stack Agentic SecOps in Action
Generate detections at the source, connect them through shared context, and accelerate triage and response across the SOC.

Tuskira’s Difference
Watch the video
See how Tuskira helps security teams validate threats, uncover breach paths, and move faster from signal to action.

