If the Attack Path Still Exists, You Haven’t Solved the Incident

Though it’s not often discussed, most environments experience repeat incidents. The initial access vector may change, yet the underlying mechanics remain familiar.
- A ransomware campaign that previously entered through a phishing foothold resurfaces months later through an exposed service, but once inside, it traverses the same lateral movement paths, abuses the same overprivileged identities, and reaches the same high-value assets.
- A privilege escalation technique that was investigated and contained reappeared in a different business unit because the entitlement model that enabled it was never structurally corrected.
- An identity abuse pattern surfaces across departments, not because analysts missed it the first time, but because the systemic reachability of that identity path was never eliminated.
- A misconfiguration that triggered an alert, generated a ticket, and was marked remediated was later exploited again in a parallel environment where the same configuration drift persisted.
These aren’t isolated operational oversights. They’re architectural signals. When the same class of incident reoccurs, even through a slightly different entry point, it indicates that the environment was restored to a stable state without being hardened against that attack pattern globally. The case was closed, the alert volume moved on, and metrics reflected progress, yet the structural breach path remained viable somewhere in the system.
When incident classes repeat, your system processes the incident, but it doesn’t learn from it.
The Three Repeat Patterns We See Most
A. Repeat Ransomware Chains
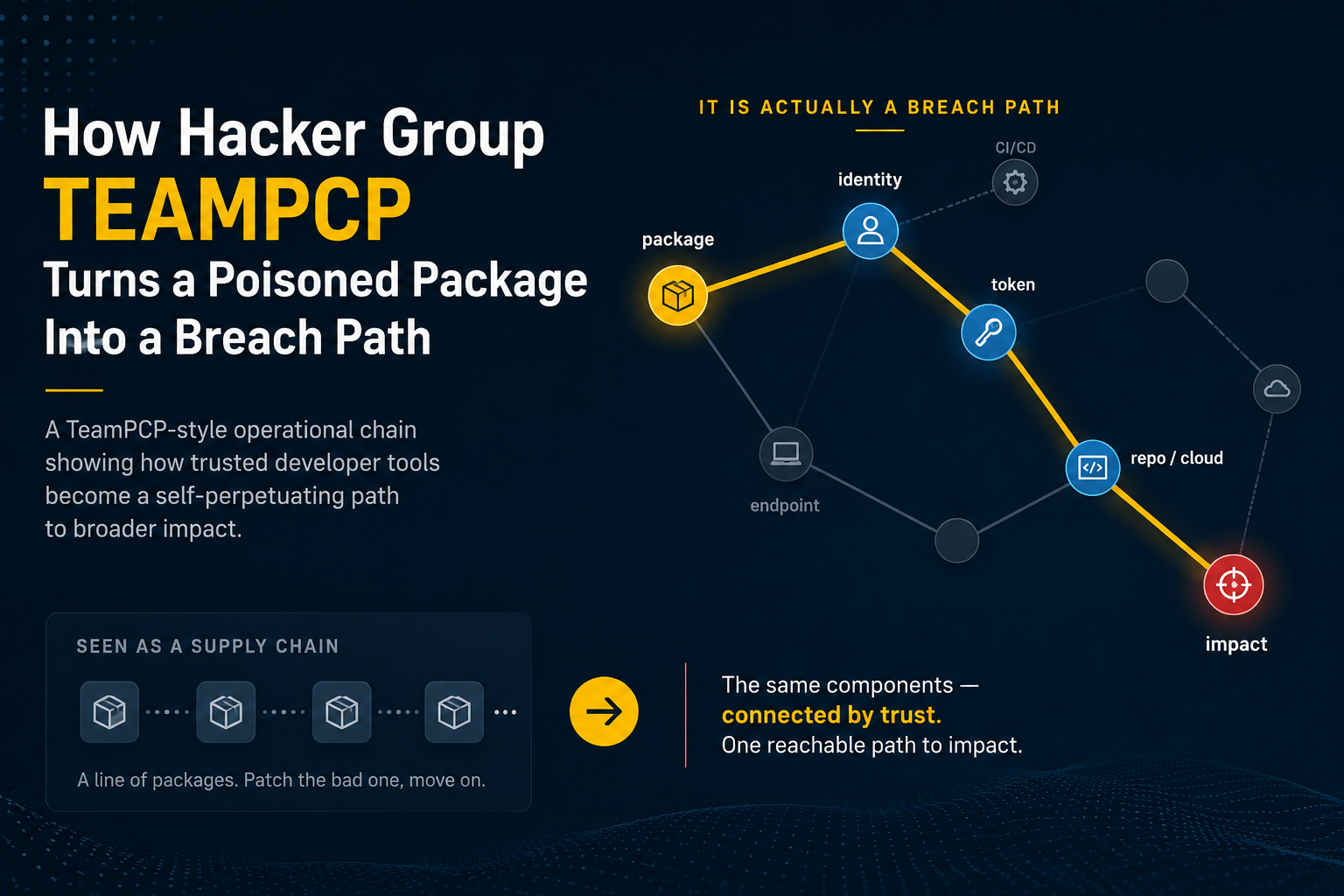
Ransomware rarely repeats in exactly the same way, but the structural path it follows often does. The initial access vector may shift from phishing to an exposed service, or from a compromised endpoint to a third-party integration, yet once inside, the attacker frequently encounters the same permissive identity relationships, the same lateral movement corridors, and the same segmentation weaknesses that enabled prior impact. The privileged account class used for escalation is often identical. The network or identity boundary that failed to interrupt the chain previously fails again, even if the entry point differs.
In post-incident reviews, teams may conclude that the new foothold was distinct and therefore unrelated to the prior case. However, when the attack chain is modeled end-to-end, the overlap becomes obvious. The reuse is not in the malware hash or delivery mechanism; it’s in the reachable privilege paths and control gaps that remain structurally intact across the environment. Containment restores operations, but it doesn’t necessarily eliminate the systemic route from initial access to sensitive assets.
B. Recurring Identity Abuse
Identity-driven incidents exhibit similar recurrence. Over-privileged service accounts, excessive role inheritance, stale credentials, and token replay conditions often remain latent even after a specific user or machine account is disabled. An investigation may identify the compromised identity and revoke access, but if equivalent roles or service accounts retain the same permissions model, the path to critical systems remains elsewhere.
IAM misconfigurations frequently survive incident response because remediation focuses on the compromised principal rather than the entitlement architecture. The affected user is disabled, the token is revoked, and the case is closed. What’s not always addressed is whether the same privilege graph is replicated across departments, business units, or environments.
Containment resolves the instance. Structural correction requires identifying and eliminating the identity path across similar roles and permission groupings so that the attack chain can’t be reconstructed with a different credential.
The graph shows how a single credential can traverse policy layers without interruption. Structural correction requires eliminating equivalent reachability across similar roles.
C. Recurrent Privilege Escalation
Privilege escalation patterns also tend to recur, particularly in hybrid and cloud environments where entitlement drift is continuous. Local administrator sprawl, IAM role chaining, and control-plane misconfigurations create predictable elevation paths. An endpoint may be isolated and reimaged, or a specific role may be adjusted, yet the broader privilege model that enabled the escalation remains partially intact.
Security response typically focuses on the affected asset. The compromised machine is contained, the immediate privilege anomaly is corrected, and monitoring rules may be updated. However, unless the underlying privilege model is hardened globally, similar escalation conditions can emerge in adjacent systems. Drift reintroduces risk. Temporary fixes don’t address systemic exposure.
Structural correction requires measuring and reducing the overall attack path count associated with privilege escalation, not just eliminating a single exploit instance. The relevant question is whether the environment now has fewer viable escalation paths than before the incident.
Why Repeat Incidents Happen
Repeat incidents are rarely the result of negligence or poor decision-making; rather, they’re a consequence of how most security programs are architected. In the typical enterprise, three core workflows operate independently:
- Exposure discovery: tools such as vulnerability management platforms, CNAPPs, and IAM reviews, identify weaknesses and assign severity, but they don’t validate how those weaknesses participate in real attack chains
- Incident response: Incident response platforms such as SIEM and EDR detect and investigate active events, contain affected assets, and close cases, yet they aren’t structurally designed to eliminate the broader paths that enabled the incident.
- Control engineering: Control engineering teams manage IAM policies, firewall rules, segmentation, and detection logic, but updates are often triggered by discrete escalations rather than continuous attack-path analysis.
These loops run in parallel. Findings are tracked. Alerts are triaged. Policies are tuned. However, the outputs of one loop rarely become systemic inputs to the others in a coordinated, automated way. A vulnerability is remediated in one environment while its equivalent persists elsewhere. An identity is disabled while similar privilege relationships remain intact. A detection rule is refined without reassessing whether the underlying path to sensitive assets is still reachable.
Without a closed-loop system, incidents are resolved locally, but vulnerabilities persist globally.
The Hidden Cost of Non-Learning Systems
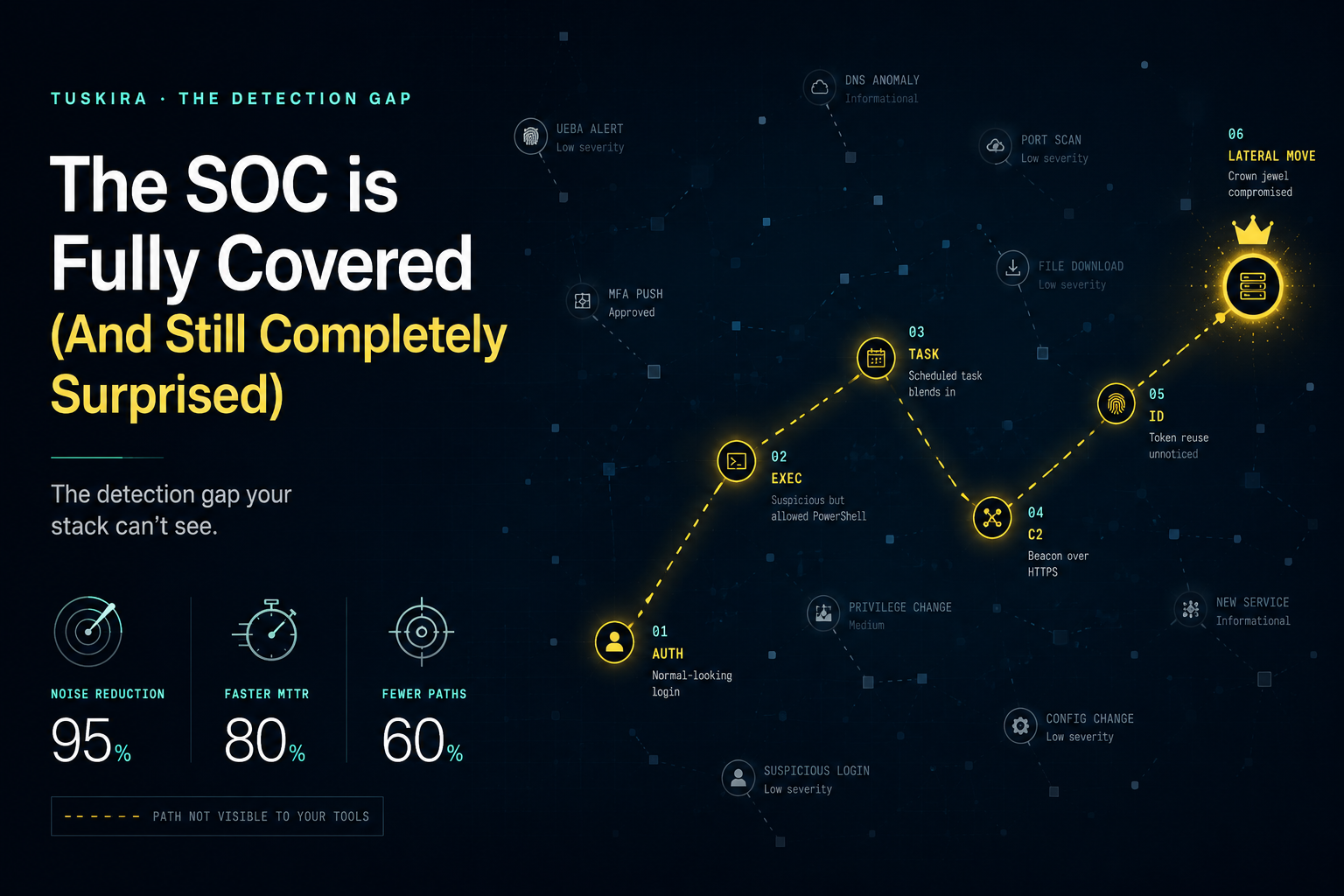
When security systems don’t structurally learn from incidents, the operational impact compounds over time. Alert volume may briefly decline after tuning exercises, but it typically plateaus or resumes rising as equivalent exposure paths reintroduce similar detection patterns. The same investigation playbooks are reused quarter after quarter because the underlying attack mechanics remain viable. Analysts become faster at handling familiar scenarios, yet the scenarios themselves don’t disappear and this creates a false sense of improvement.
Triage accelerates, automation reduces handling time, and escalation pathways become more efficient; however, the environment’s structural attack surface remains largely unchanged. Identity reachability persists. Privilege escalation routes remain available. Segmentation gaps continue to allow lateral movement. The organization becomes better at processing incidents without materially reducing the conditions that generate them.
Over time, analyst fatigue increases because the work becomes cyclical rather than corrective. Experienced responders recognize recurring patterns but lack a systemic mechanism to eliminate them globally, and as a result, staffing and budget scale in proportion to alert volume. More detections require more review capacity. More tools generate more signals. Cost grows linearly with operational load.
Throughput improves. Breach probability doesn’t.
What a Learning Security System Looks Like
A learning security system is not defined by faster triage or better dashboards. It is defined by whether each incident measurably reduces future attackability.
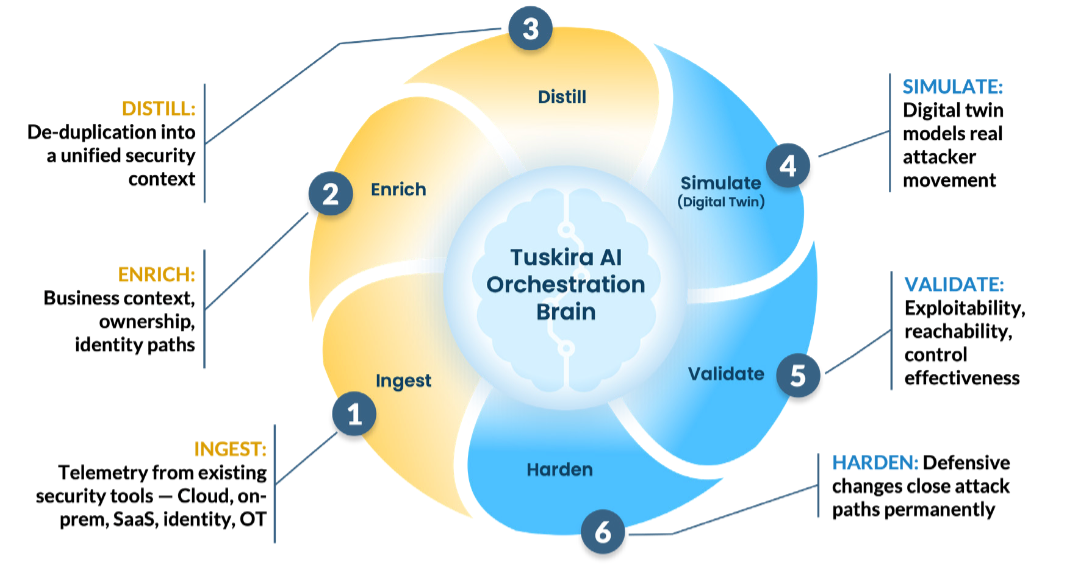
1. Ingest: Unified Telemetry Collection
The system continuously ingests telemetry from existing security tools and infrastructure across cloud, on-prem, SaaS, identity, and endpoint environments. This includes detections, exposure findings, identity relationships, configuration state, and control metadata. The objective is not aggregation for reporting, but structured input for attack-chain reasoning.
2. Enrich: Contextual Expansion
Raw signals are enriched with business context, ownership metadata, identity relationships, asset criticality, and dependency mapping. This transforms isolated alerts or findings into context-aware entities that reflect how systems actually interconnect.
An alert tied to a VM becomes:
• An identity path
• A network position
• A privilege boundary
• A business function
Without enrichment, breach path modeling is incomplete.
3. Distill: De-Duplication into a Unified Security Graph
Signals are normalized and deduplicated into a unified attack-chain graph. Overlapping findings, redundant alerts, and parallel exposure signals are reduced into a coherent representation of reachable paths.
This step prevents the system from reacting to noise and ensures it reasons over structure rather than volume. The outcome is a consolidated graph of assets, identities, permissions, controls, and reachable paths.
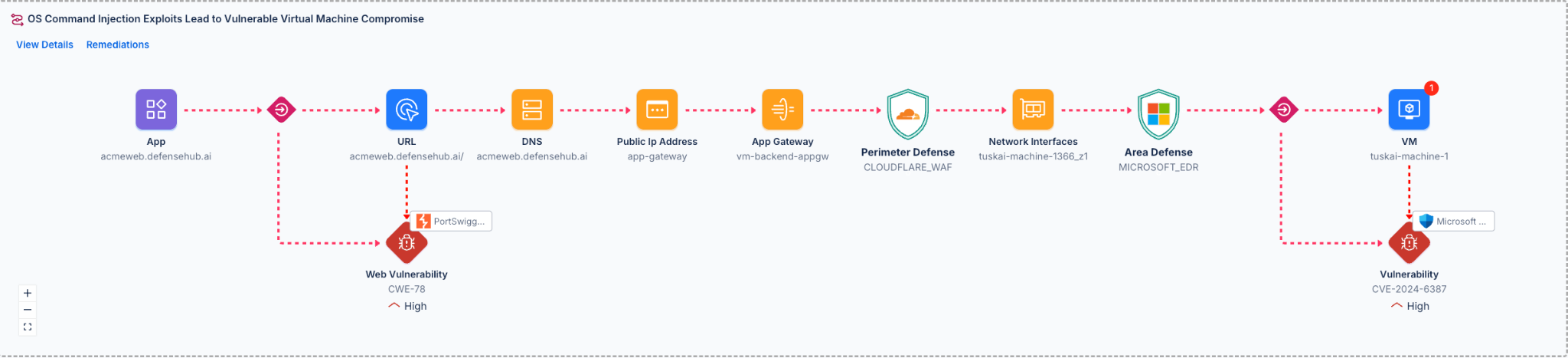
4. Simulate: Model Real Attacker Movement
Using the unified context model, the system simulates attacker movement across identity, network, and workload boundaries. This is where each confirmed incident is mapped to a validated breach path.
The simulation answers:
• How did the attack succeed?
• What control layers were bypassed?
• What privilege relationships enabled movement?
This step transforms an incident into a structural map.
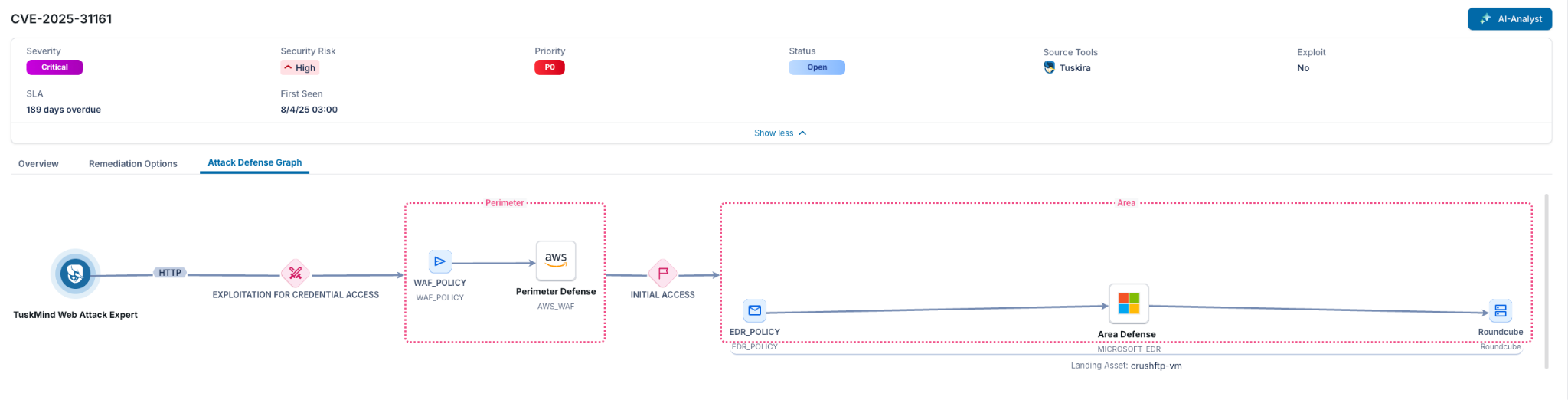
5. Validate: Confirm Reachability and Control Effectiveness
The system evaluates whether the mapped breach path, or structurally equivalent paths, remain reachable elsewhere in the environment.
It determines:
• Exploitability
• Reachability
• Whether existing controls interrupt the path
• Whether equivalent identity or privilege routes exist in parallel environments
This prevents local containment from masquerading as systemic correction.
6. Harden: Apply Systemic Control Corrections
Finally, defensive changes are applied at the policy level to eliminate the class of path, not just the instance.
This may include:
• IAM role correction
• Segmentation refinement
• Firewall policy updates
• Detection logic improvements
• Compensating control deployment
Hardening is measured by a reduction in reachable breach path count and recurrence potential.
The updated control state and detection logic are incorporated into the telemetry ingested in the next cycle, ensuring the system improves structurally over time.
Enabling this loop requires a unified context model for assets, identities, controls, and telemetry, often implemented as a continuously updated digital twin that models attack chains. It requires policy-bounded automation capable of safely applying control changes and a structured feedback mechanism that converts investigative findings into reusable intelligence across the environment.
The Metric That Matters for Structural Improvement
Security programs measure many things: alert volume, mean time to respond, case closure rates, and patch SLAs. These metrics describe activity, but they don’t necessarily describe structural improvement.
A learning security system must be evaluated on whether it reduces recurrence and reachability over time, and that requires tracking metrics tied to attack mechanics.
- First, repeat incident class frequency should decline. If ransomware, credential abuse, or privilege escalation patterns reappear at the same rate quarter after quarter, the underlying conditions that enable them remain intact.
- Second, reachable breach path count should trend downward. This reflects the number of viable attack chains from initial access to sensitive assets under current identity, network, and control conditions. If that number is static, risk posture is static.
- Third, control interruption coverage should increase. Controls should demonstrably interrupt realistic attack chains across identity and network boundaries, not simply exist as policy artifacts.
- Fourth, incident recurrence rate per attack pattern should fall as structural hardening is applied. Similar techniques should become harder to reuse because equivalent paths have been eliminated globally.
These metrics move the conversation from operational efficiency to structural risk reduction, answering: Is the environment becoming less attackable over time?
And ultimately, you know, if repeat incidents aren’t trending downward, your system isn’t improving.