Does the Reported Iran-Linked Stryker Attack Highlight a Growing SecOps Problem?
Public reports this week indicate that Stryker, a world-leading medical technology company, is experiencing a global network disruption tied to a cyberattack. The Iran-linked group Handala has claimed responsibility and said it wiped systems and extracted data, while Stryker has publicly stated that it’s experiencing a disruption to its Microsoft environment, believes the incident is contained, and has “no indication of ransomware or malware.” Because the incident is still unfolding, many of the attacker’s claims remain unverified. At the same time, Stryker’s public response appears to show swift containment and communication under difficult circumstances.
In incidents like this, the first challenge is understanding what actually happened across systems that were never designed to be investigated as one environment.
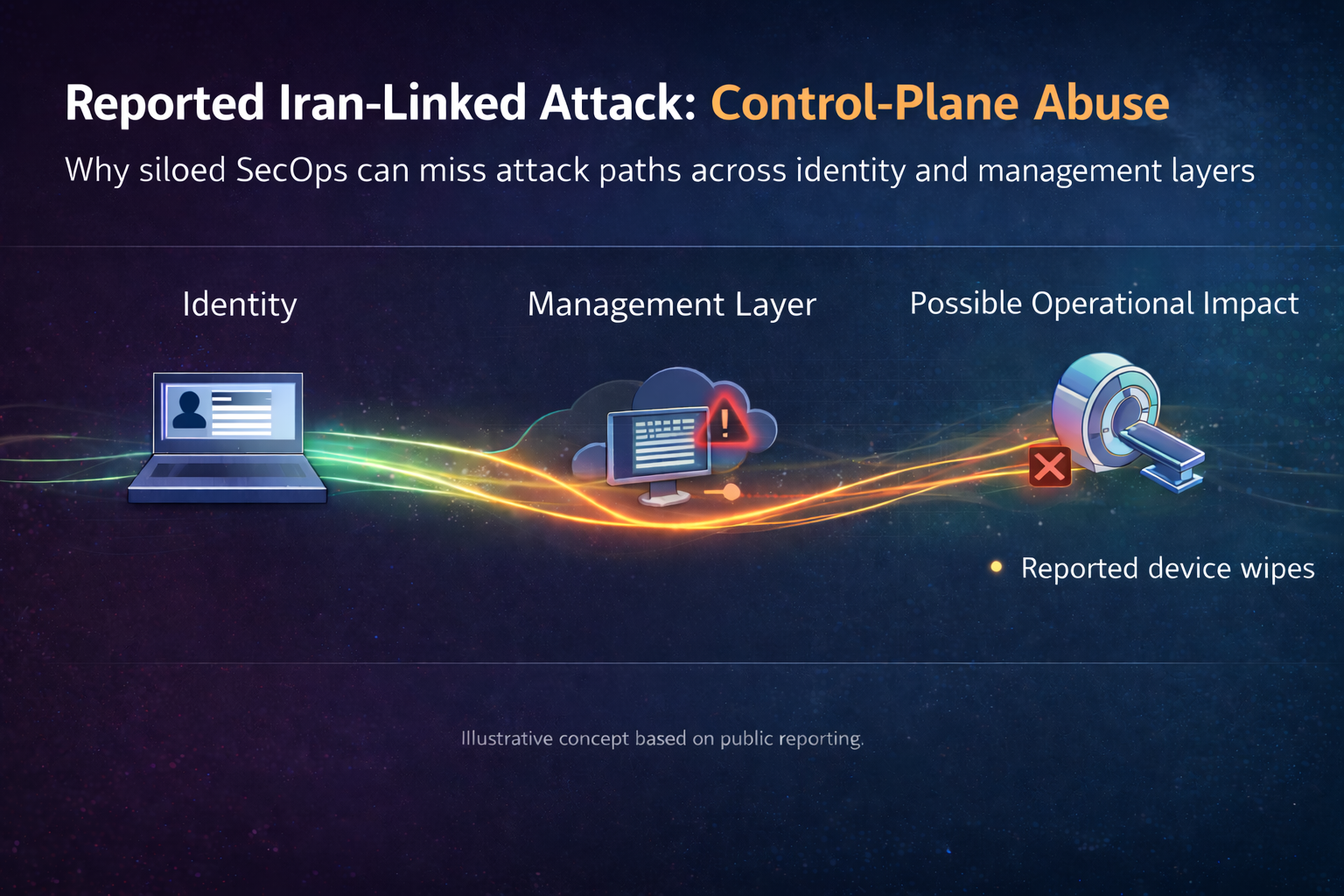
Early reports and employee discussions cited disruptions to Microsoft-connected systems, device wipes, and possible use of Microsoft Intune to issue remote-wipe commands. Krebs reported that a source familiar with the incident believed Intune may have been used, while Reddit discussions from people claiming to be employees described phones and endpoints being wiped and urged coworkers to remove Intune-related tooling. Those community reports aren’t authoritative evidence on their own, but taken together with Stryker’s statement, they point to an attack pattern that may involve abuse of a management or control layer rather than a simple malware outbreak on isolated endpoints.
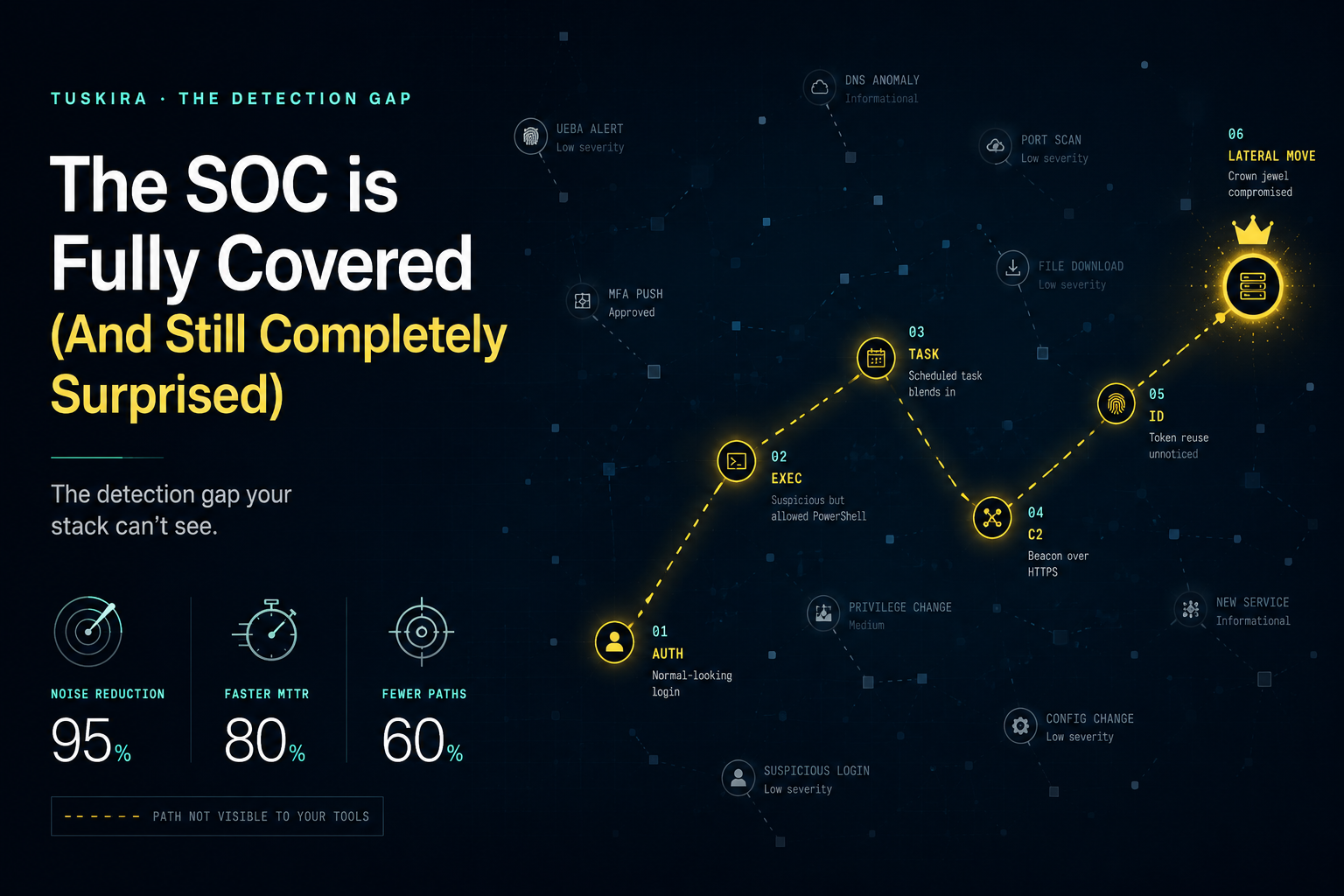
Most security teams are still organized around siloed detections: endpoint in one console, identity in another, cloud in another, device management somewhere else, and key administrative actions buried in logs that may not be centralized or prioritized. When an attacker abuses legitimate control surfaces such as identity, MDM, SaaS administration, or other management infrastructure, the activity can look benign in isolation while the real attack path unfolds across multiple systems. This is why static detection workflows break down.

Traditional detection engineering is the manual process of centralizing logs, writing rules to catch suspicious behavior, and tuning those rules over time based on investigation outcomes. But attacks that move through distributed systems don’t wait for perfect ingestion or manual correlation. By the time analysts connect endpoint behavior, identity events, management actions, and infrastructure context, the disruption may already be underway. Threats change in minutes & hours, while detection engineering is typically updated in days and weeks.
The broader lesson from the Stryker incident is twofold. First, the company appears to have moved quickly, which is reassuring in a high-disruption scenario. Second, modern disruptive attacks increasingly appear to move through the control plane: identity systems, management infrastructure, federated cloud and SaaS environments, and trusted administrative paths. That changes what good detection has to look like.
Security teams need to be able to:
- Generate detections across distributed sources where the relevant telemetry already lives
- Correlate those detections with identity, asset, infrastructure, and control context
- Distinguish true threats from benign administrative behavior or misconfiguration
- Continuously refine rules and response actions based on validated outcomes
This is the shift the market is beginning to see from static, centralized detection to federated threat detection.
Public reporting on Handala also reinforces the broader threat trend. Palo Alto Networks’ Unit 42 has linked Handala to Iran’s MOIS-aligned ecosystem and described recent Iranian-aligned activity as opportunistic, fast-moving, and often designed to create disruption and intimidation. In that kind of environment, detection quality matters more than alert volume, and context matters more than log accumulation.
The Stryker incident is still developing, and it would be premature to claim that any vendor could have definitively prevented this specific event. But it’s already a useful reminder that modern attacks don’t stay on the endpoint. They move through the systems that manage the enterprise. And SOCs that still rely on static rules, siloed context, and centralized log dependency will keep finding out too late.