AI Just Learned to Hack, And Defenders Should Be Excited.
How Anthropic’s Mythos Preview Changes the Calculus of Cybersecurity, and Why Continuous Threat Exposure Management Is the Answer
By Piyush Sharma | CEO & Co-Founder, Tuskira | April 8, 2026
On April 7, 2026, Anthropic published what may be the most consequential cybersecurity research of the decade. Their Claude Mythos Preview model autonomously discovered zero-day vulnerabilities in OpenBSD that had been hiding for 27 years, wrote functional browser exploits that chained four separate vulnerabilities into a sandbox escape, and reverse-engineered stripped binaries to find flaws in closed-source software. All for under $50 per run.
The industry reaction has been predictable: alarm about AI-powered attacks, questions about whether defense can keep pace, and uncertainty about what it means for security investments already in motion.
We see it differently. Mythos isn't a threat to defenders. It's the strongest possible validation that the era of continuous, AI-native security has arrived, and that organizations still operating on periodic assessment cycles are running out of time.
The Numbers That Matter
Before we discuss implications, let’s ground ourselves in what Mythos actually demonstrated:

These aren't incremental improvements. This is a capability discontinuity. The economics of vulnerability discovery have permanently shifted.
The Real Threat Isn’t Mythos Itself
Mythos Preview is restricted to Anthropic’s Project Glasswing partners — critical infrastructure defenders and open-source maintainers. It won be released publicly.
But here’s what the announcement actually tells us: today’s generally available frontier models are already capable of meaningful vulnerability discovery. Anthropic notes that Opus 4.6 successfully found exploitable bugs in Firefox. The gap between “publicly available” and “Mythos-level” will close within 12–18 months as model capabilities advance across the industry.
The question isn't whether AI-discovered zero-days will affect your organization. The question is whether you'll discover your exposures before adversaries discover your vulnerabilities.
This creates five cascading effects for every organization:
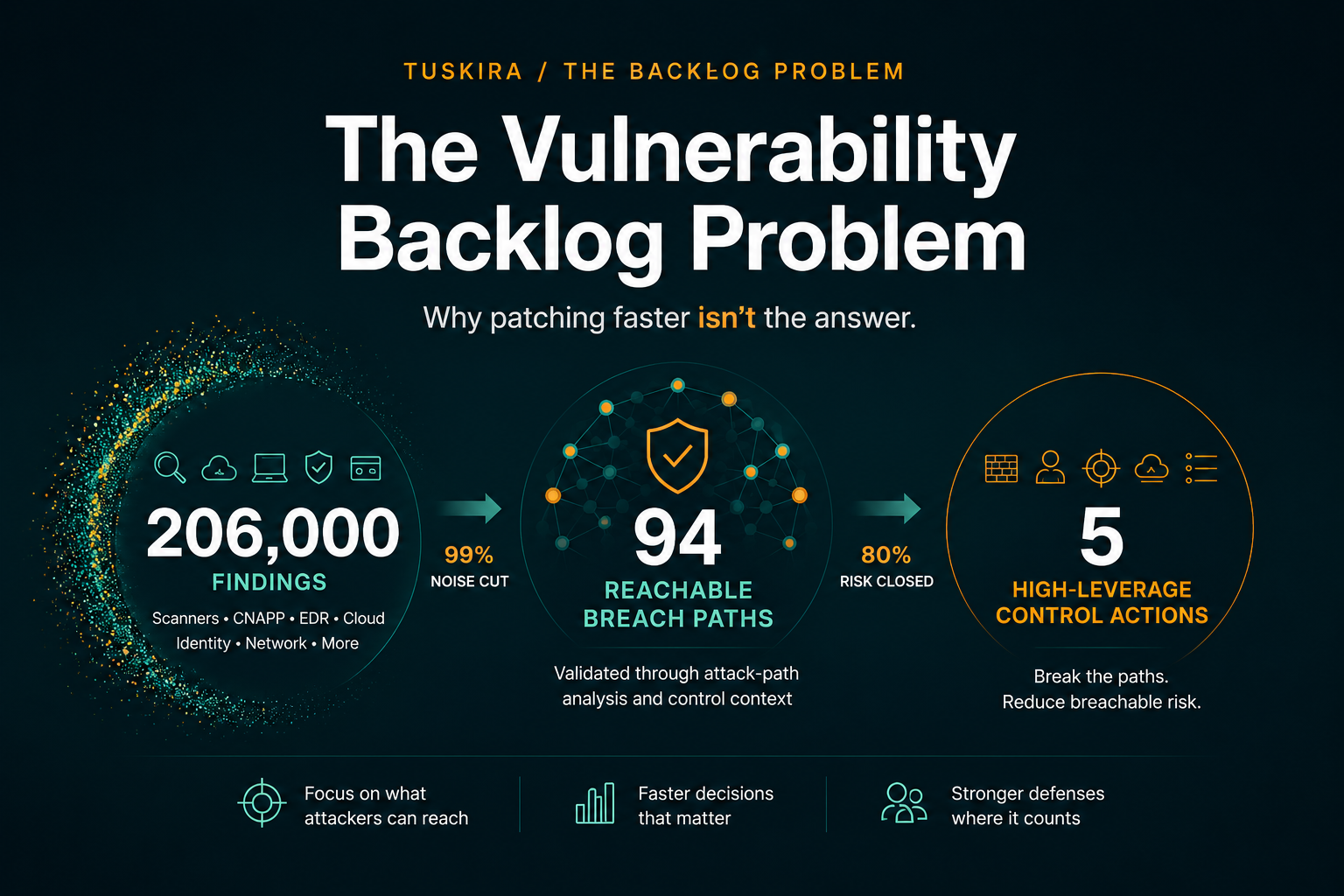
- Vulnerability volume explodes. When finding a zero-day costs $50 instead of $50,000, the raw number of disclosed CVEs will grow by orders of magnitude. Your vulnerability backlog, already measured in tens of thousands, will become unmanageable through manual processes.
- Patch windows collapse. If AI can independently discover the same vulnerability that a researcher discloses, the race between patch and exploit shrinks from months to days. Organizations relying on 30–90 day patch cycles are accepting breach as inevitable.
- Attack democratization accelerates. Nation-state capabilities at commodity prices mean mid-tier criminal groups and opportunistic attackers can go after any target. The “we’re not big enough to be targeted” defense is over.
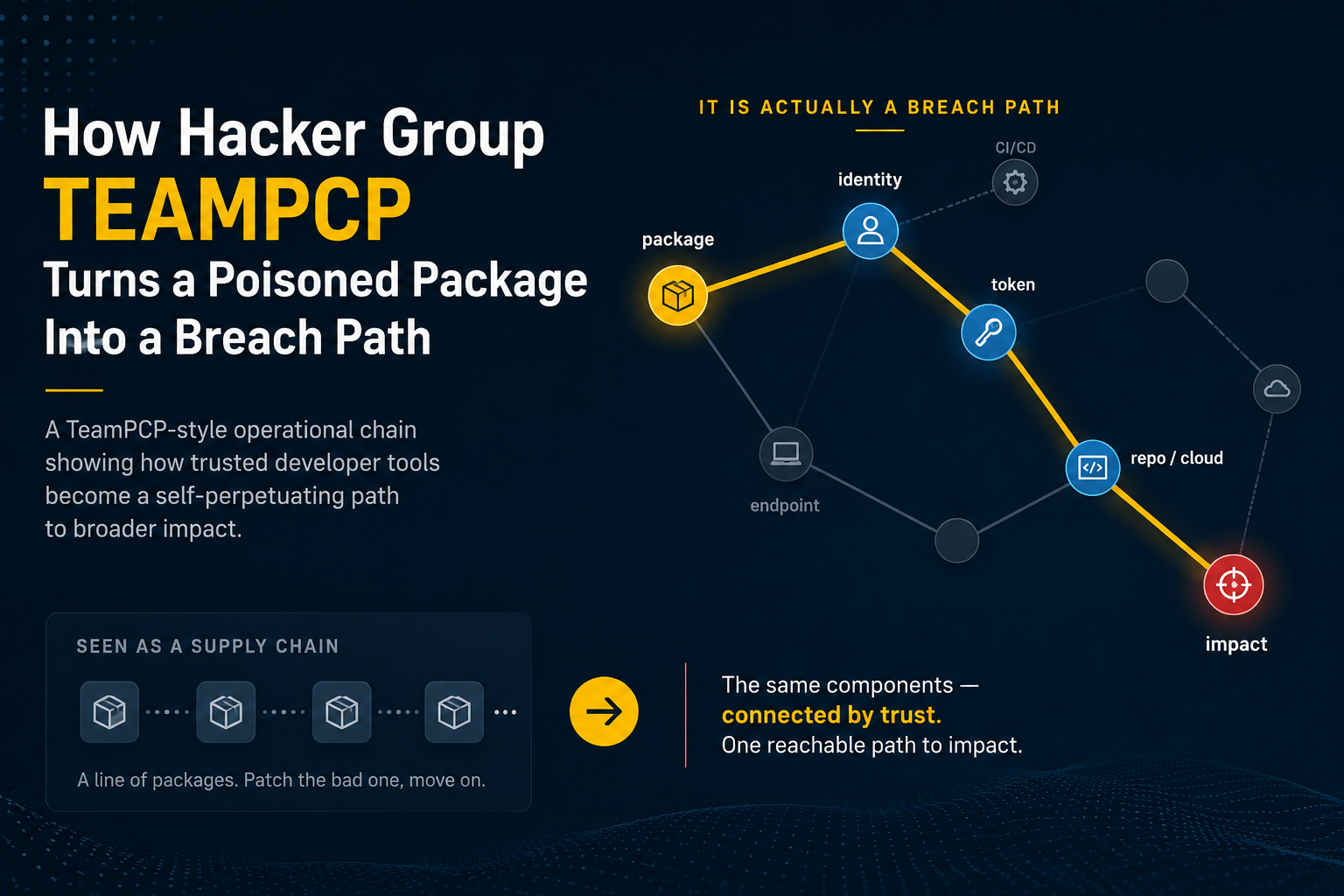
- Exploit chains become the norm. Mythos chained four vulnerabilities into a single sandbox escape. AI-generated attacks will routinely combine multiple weaknesses, a misconfiguration here, a missing patch there, an exposure path elsewhere , into compound attack chains that no single-domain scanner can detect.
- Defense-in-depth is validated. Crucially, Anthropic’s own research showed that Linux kernel hardening (SMEP, SMAP) successfully prevented exploitation even when Mythos found the zero-days. Properly configured compensating controls work. But only if you know they’re actually applied.
Why Defenders Should Be Excited, Not Afraid
The same AI capabilities that enable Mythos are available to defenders today, and defenders have a structural advantage: access to their own data.
An attacker using Mythos works from the outside in: scanning public surfaces, guessing at internal topology, hoping misconfigurations create a path. A defender using AI works from the inside out: full visibility into every asset, every configuration, every relationship, every vulnerability, every control policy.
This asymmetry is decisive when combined with continuous AI-native analysis. Here is what becomes possible:
Preemptive Attack Surface Discovery
Instead of waiting for scanners to flag known CVEs, AI agents can continuously mine raw configuration data from every provider in your environment (cloud, endpoint, identity, network) to discover exposure paths that haven’t been cataloged yet. A public IP bound to a NIC on a VM in a subnet with no network security group is an exposure, whether or not a CVE exists for the software running on that VM.
Compound Risk Assessment
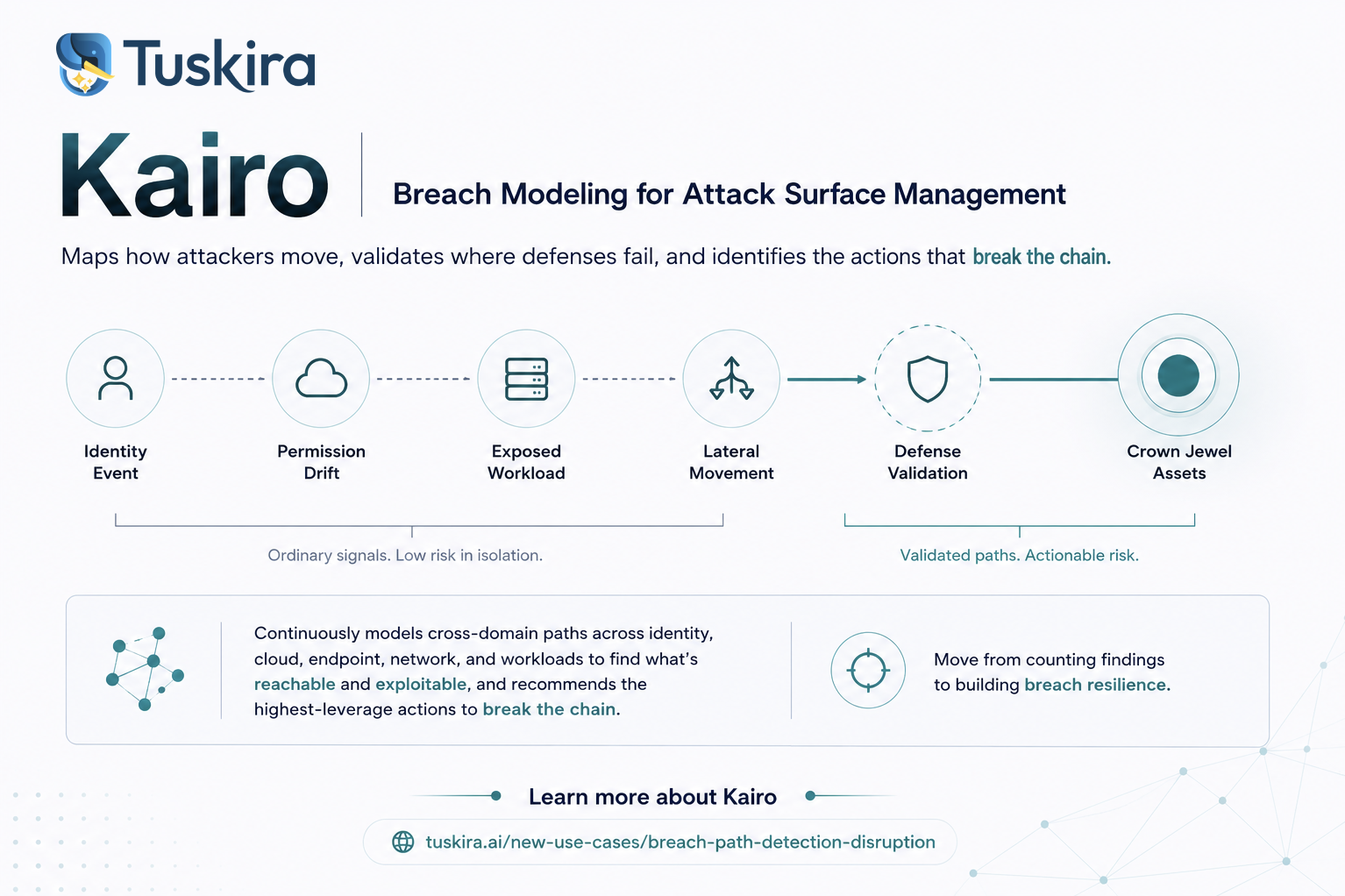
AI can correlate across domains in ways humans can't maintain at scale. A vulnerability on a domain controller (from your vulnerability scanner) + an unprotected subnet (from your cloud configuration) + a VPN hybrid path bridging cloud and on-prem (from your network topology) = a critical compound risk that no individual tool would flag. Continuous cross-domain synthesis makes these invisible attack chains visible.
Exploitability-Aware Prioritization
CVSS scores treat every vulnerability in isolation. AI-native analysis can assess: Is this asset internet-exposed? Does it have compensating controls (EDR, WAF, NSG)? Are those controls properly configured? Is it on a viable attack path? Are there known exploits? This turns a flat list of 47,000 findings into a ranked shortlist of the 50 that actually matter.
Continuous Attack Path Reconstruction
As new vulnerabilities are disclosed (and the pace will accelerate), attack paths change. A path that was blocked yesterday by a patched intermediate host becomes viable when a new zero-day affects that host. Continuous reconstruction identifies which new paths are viable in hours, not quarters.
Mythos-for-Mythos: Turning Offense Into Defense
The ultimate response to AI-powered offense is AI-powered defense running the same playbook: discovering vulnerabilities, assessing exploitability, tracing attack chains, and identifying chokepoints, but doing it on your environment first, continuously, and feeding the results directly into remediation workflows.
The organizations that thrive in the post-Mythos era won't be the ones with the biggest security teams. They'll be the ones with the most continuous, AI-native understanding of their own attack surface.
What Security Leaders Should Do Now
Mythos-class capabilities will become widespread within 12–18 months. The preparation window is now. Five concrete steps:
- Shrink your exposure surface immediately. Audit and reduce internet-facing assets. Every public IP, every web app without HTTPS enforcement, and every storage account with allow-all network rules are potential entry points for AI-discovered zero-days. This is the highest-ROI defensive action available today.
- Move from periodic to continuous assessment. Annual pentests and quarterly scans can't keep pace with AI-speed vulnerability discovery. Deploy AI-native continuous threat exposure management (CTEM) that reassesses your attack surface as new intelligence arrives.
- Prioritize by attack path, not CVSS score. In a world of abundant zero-days, the right question isn't “which CVE has the highest score?” but “which remediation breaks the most attack paths?” Chokepoint-based prioritization yields 10x better outcomes than severity-based prioritization.
- Verify your defense-in-depth actually works. Mythos’s own research proved that defense-in-depth stops exploitation. But the controls have to be applied. Confirm your EDR policies are enforced (not just assigned), your NSGs are attached (not just created), and your WAF rules are active (not just configured).
- Build cross-provider visibility now. Attackers don’t respect tool boundaries. An exposure discovered in Azure, exploited through a vulnerability found by Rapid7, on a host monitored by CrowdStrike, traversing a VPN to on-prem Active Directory... this is a single attack chain that spans five tools, but your defense must see it as one.
The Opportunity in Front of Us
Mythos is a wake-up call, but it's also a gift. It tells us precisely what the near-future threat looks like: faster, cheaper, more sophisticated attacks that chain multiple weaknesses into compound breaches. And it tells us precisely what works against them: defense-in-depth, continuous assessment, cross-domain correlation, and AI-native analysis.
The defenders who internalize this message and act now won't merely survive the post-Mythos era. They will have the most comprehensive, continuously validated security posture their organizations have ever had.
The AI revolution in cybersecurity isn't a threat to be feared. It's a capability to be seized.
—
Piyush Sharma is CEO and Co-Founder of Tuskira, a continuous threat exposure management platform that uses AI agents to autonomously discover, correlate, and prioritize security exposures across the full technology stack.