Tuskira Recognized in Lastest Gartner Report on Preemptive Exposure Management
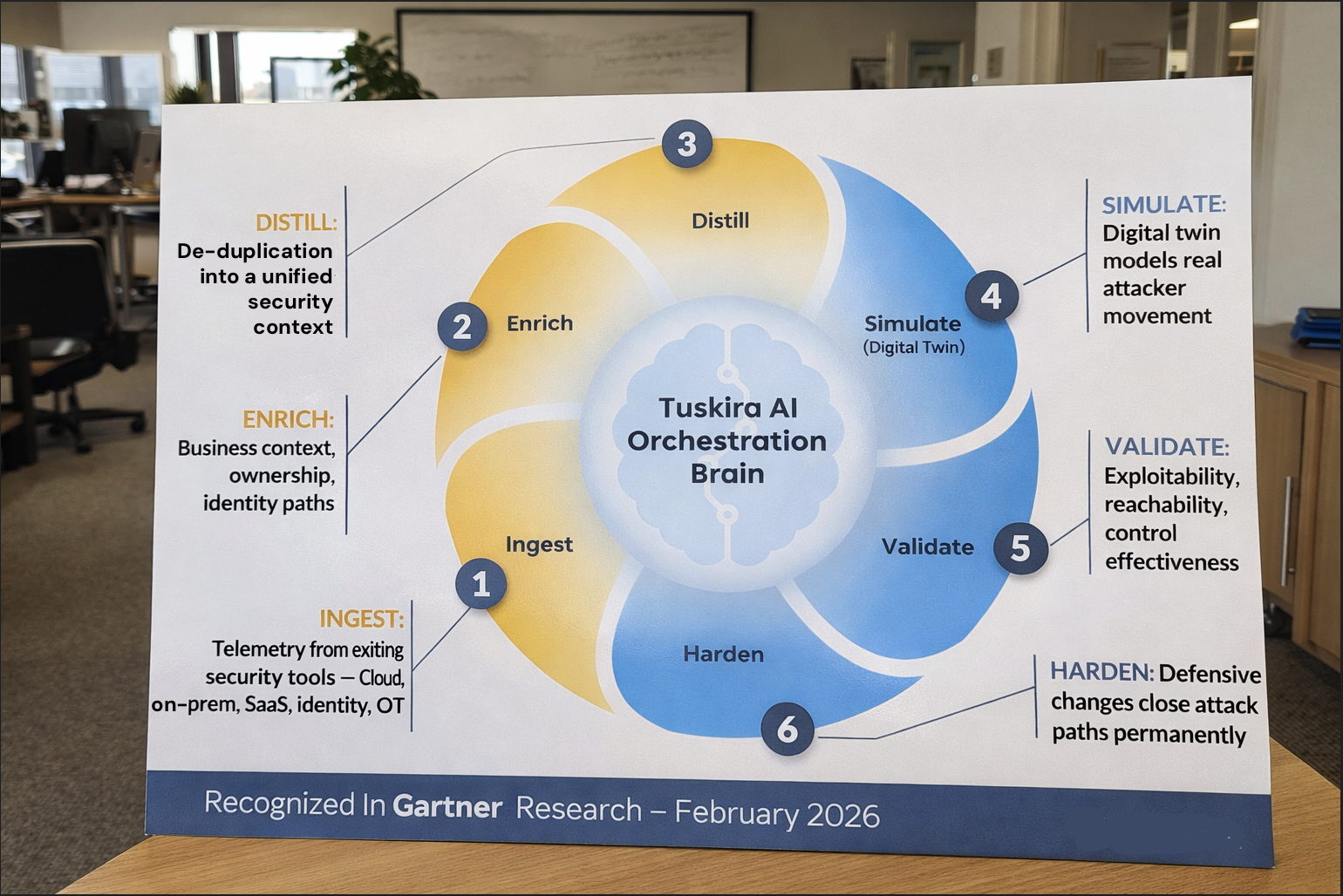
Tuskira has been recognized in Gartner’s February 2026 research note, “Emerging Tech: The Future of Exposure Management Will Be Preemptive — Driven by Autonomous Interdiction.”
The report discusses environments shaped by AI-driven, subsecond exploitation, where exposure management can’t remain a discovery-and-prioritization exercise. It must evolve into an architecture capable of validating exploitability and executing mitigation before attackers can act.
The shift from monitoring exposure to neutralizing exploitable paths defines Preemptive Exposure Management.
From Managing Findings to Proving Exploitability
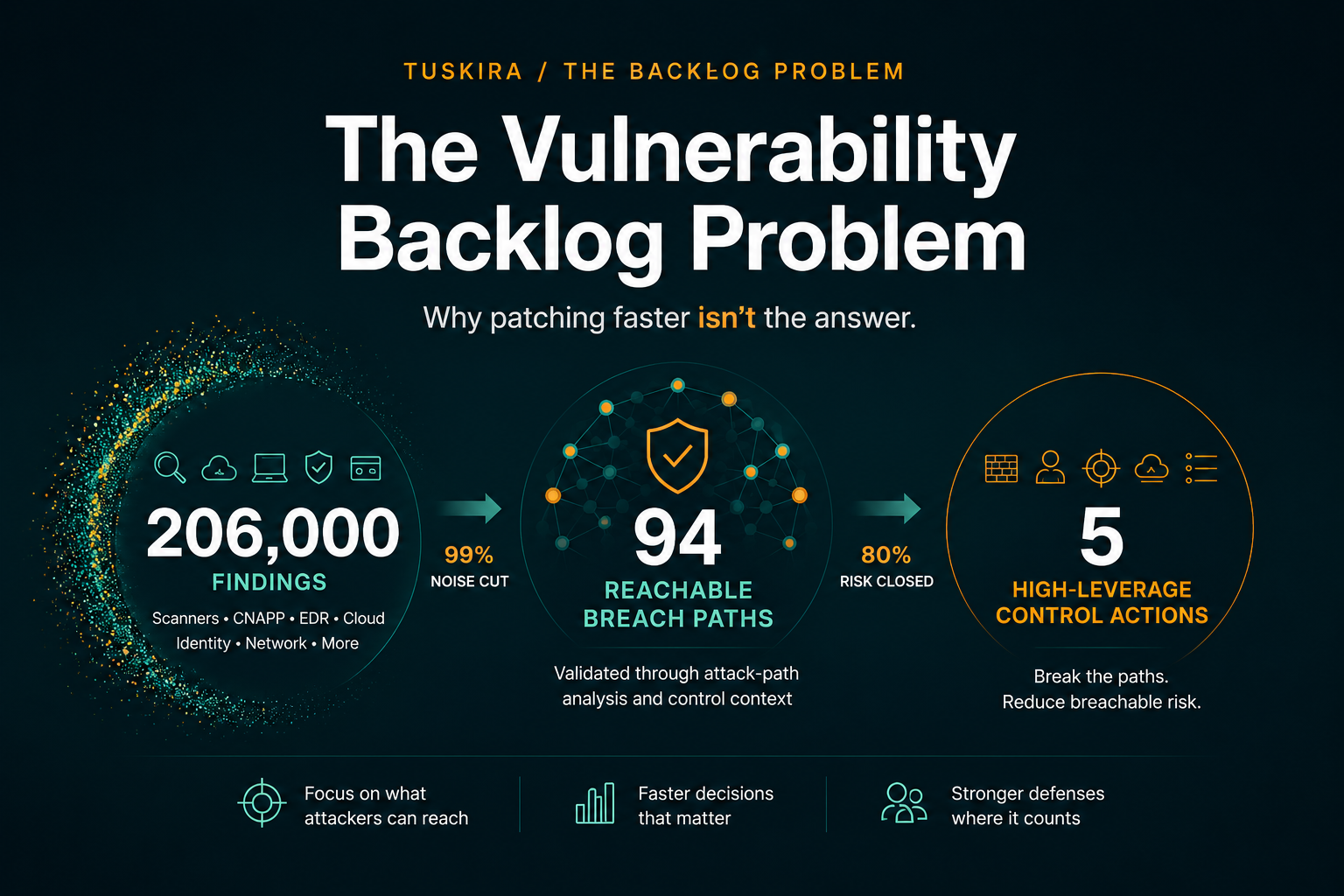
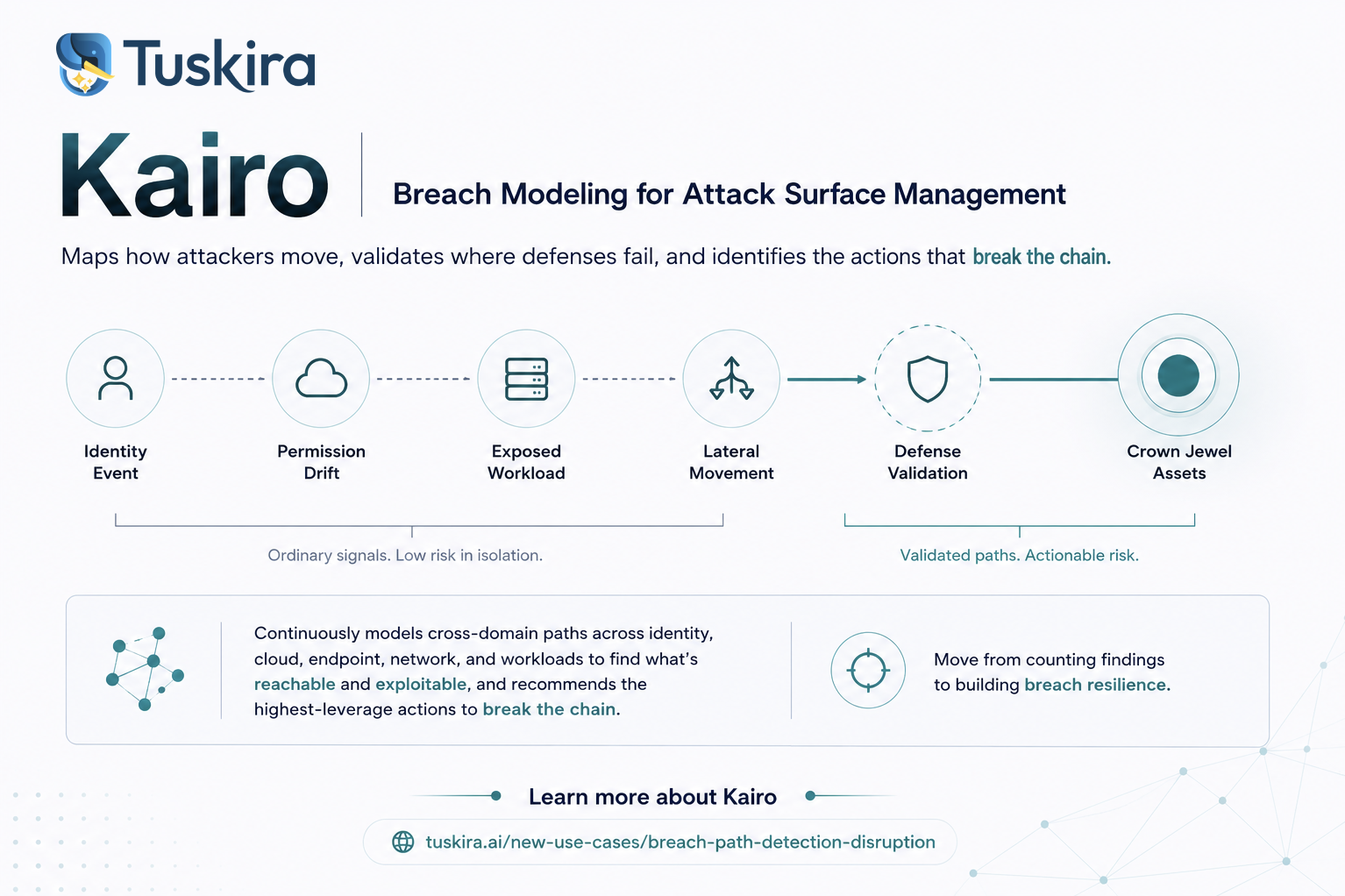
Traditional exposure management has centered on discovering vulnerabilities, assigning severity, generating tickets, and tracking remediation status. Gartner’s framing reflects a different direction. Preemptive exposure management requires continuous validation of what is actually reachable in the current environment and the ability to execute containment or control changes at machine speed, while adhering to policy guardrails and human oversight. This is a structural shift toward continuous validation and closed-loop mitigation.
How Tuskira Aligns
Tuskira was built around this architectural premise. We ingest telemetry and context from existing security investments, including SIEM, EDR, cloud platforms, identity systems, AppSec tools, CMDB, and third-party integrations. That data is distilled into a unified security context that models:
- Assets
- Identity relationships and permissions
- Control coverage
- Vulnerabilities and misconfigurations
- Network reachability
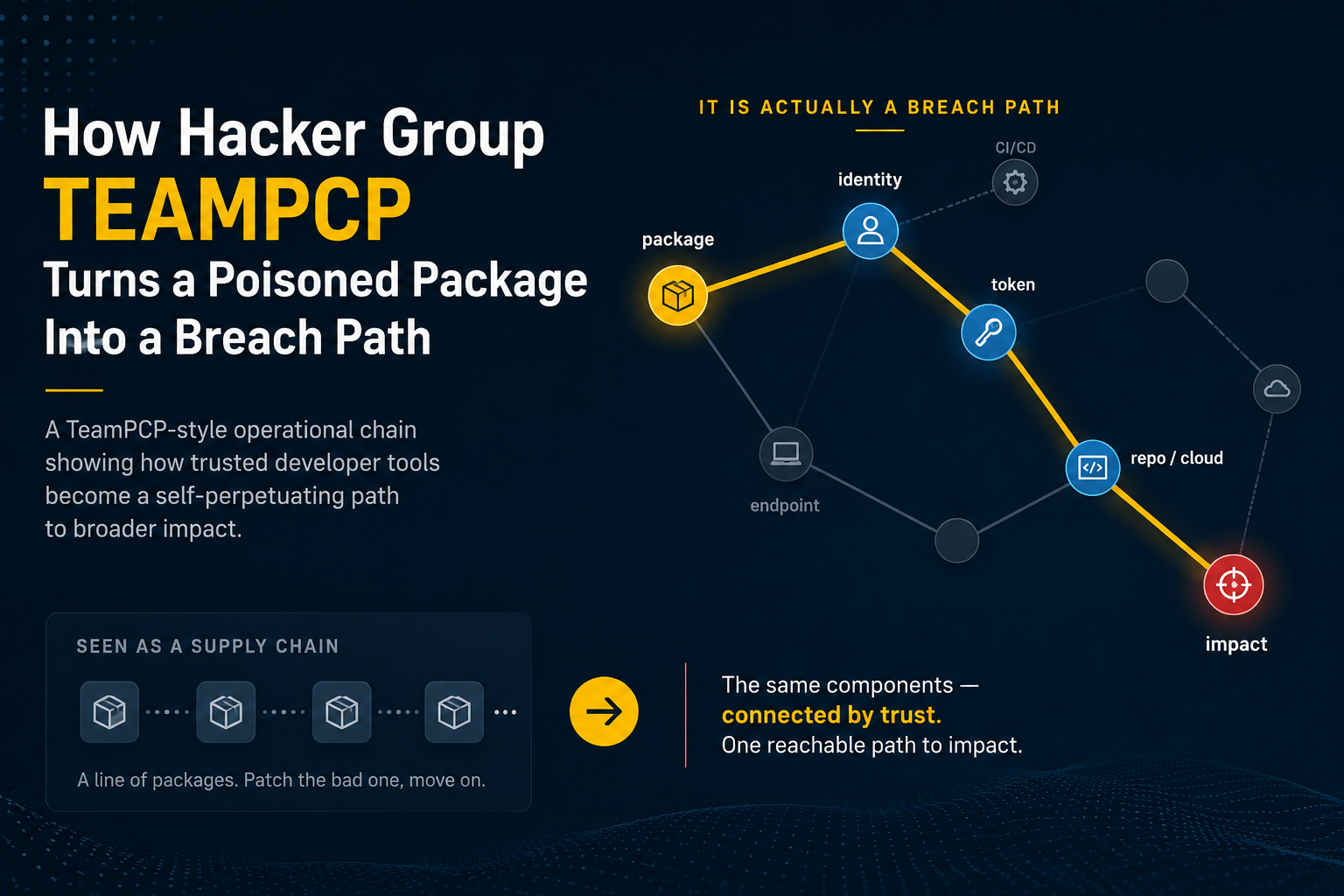
Rather than evaluating these signals in isolation, Tuskira continuously simulates attacker movement within a digital twin of the environment. Attack paths are validated based on real reachability and control effectiveness, not theoretical severity.
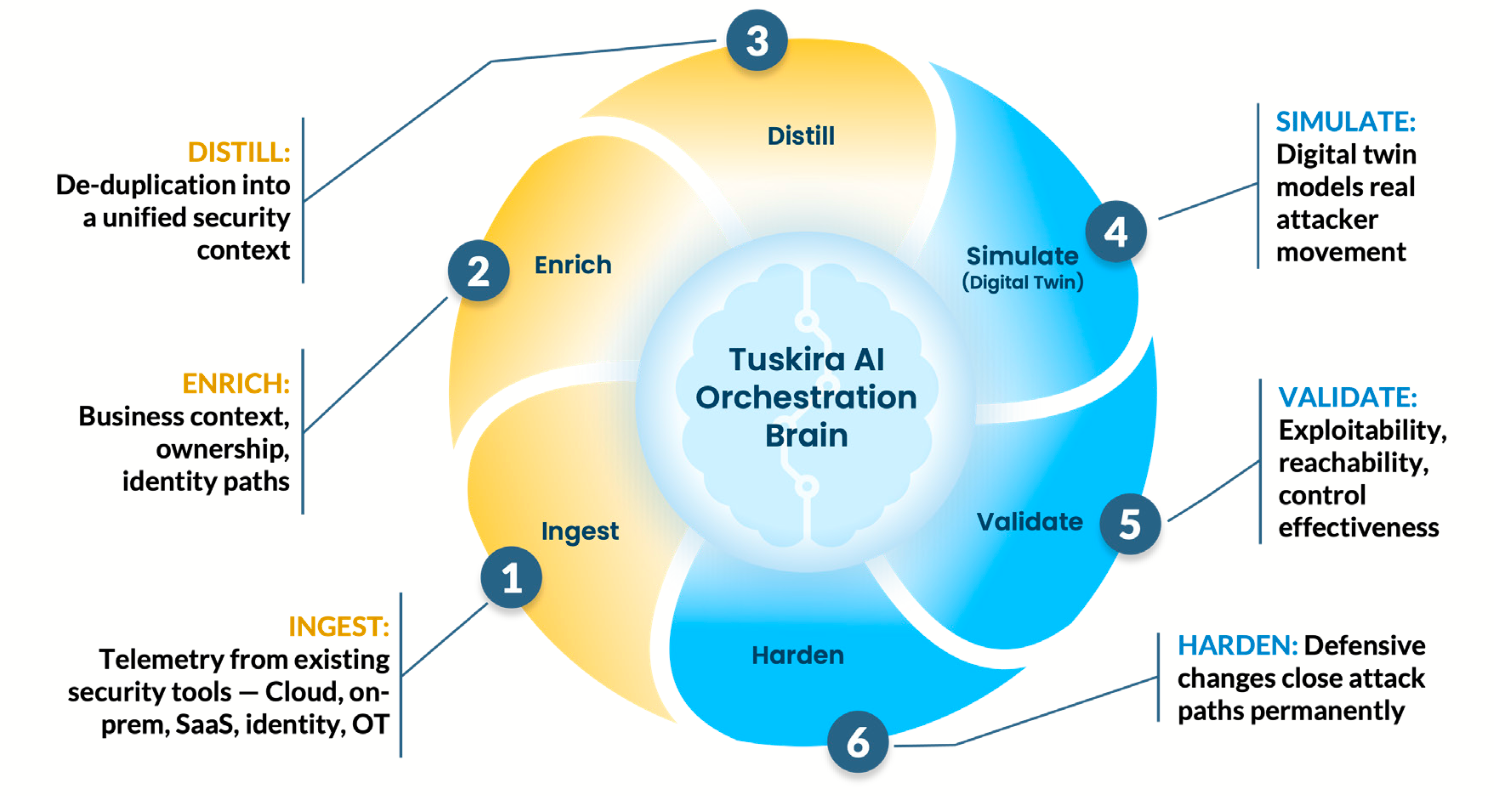
If a path is reachable, the platform executes defense-first mitigation such as IAM policy adjustments, firewall rule changes, EDR containment, WAF updates, or cloud policy hardening within customer-defined guardrails.
The objective isn’t to close tickets; it’s to permanently close attack paths. Every investigation and mitigation feeds back into the exposure model, reducing the number of repeat incident classes over time.
Closed-Loop Autonomous Defense
Gartner emphasizes the shift from human-in-the-loop to human-on-the-loop oversight, which is important because preemptive exposure management doesn’t eliminate human judgment. It shifts human focus from manual triage and correlation toward governance, exception handling, and strategic oversight while the system continuously validates exploitability and enforces control changes at machine speed.
In operational terms:
- Exposure is prioritized by what’s actually reachable.
- Control effectiveness is validated continuously.
- Mean Time to Neutralize replaces time-to-patch as a meaningful metric.
- Repeat attack paths decline because root conditions are hardened.
The Broader Market Direction
Gartner outlines a trajectory toward unified platforms that combine exposure validation, intelligent simulation, and autonomous mitigation. In the near term, the report anticipates widespread adoption of AI agents capable of independently assessing vulnerabilities and initiating mitigating responses.
Fragmented tooling and periodic assessment models won’t scale against AI-enabled adversaries. Continuous validation and closed-loop control hardening will become the baseline expectation.
Being named in this research validates the architectural direction we’ve taken, but more importantly, it reinforces what security leaders are already experiencing: managing exposure is no longer sufficient. Proving exploitability and eliminating attack paths before they’re reused is the new standard.
Preemptive exposure management is about continuously reducing reachable risk. That’s the future Gartner describes. That’s the system we’ve built. If you’re evaluating how your exposure management strategy aligns with this shift, we’d welcome the conversation.